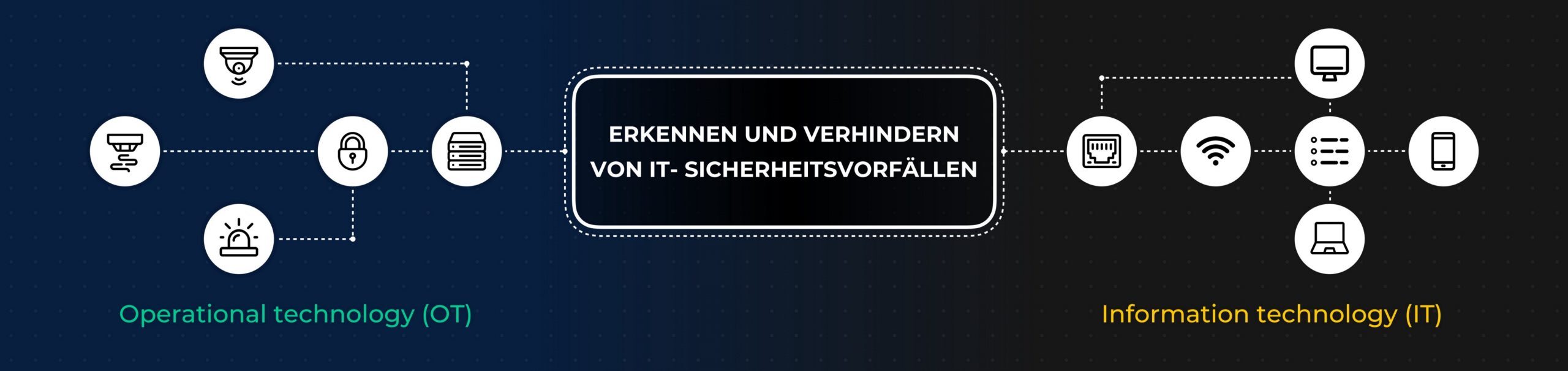
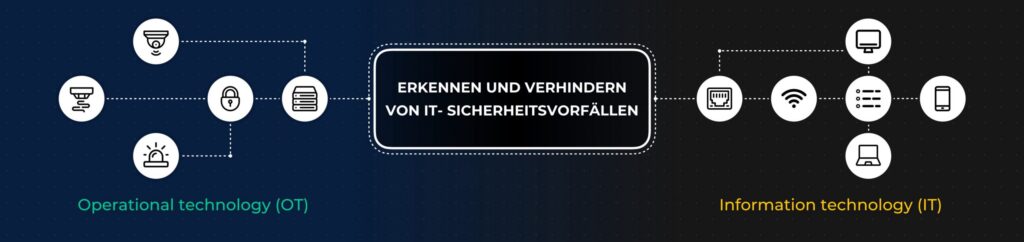
IT (Information Technology) and OT (Operational Technology) have always been considered separately from each other. They perform their respective tasks in peaceful coexistence, but there are few points of connection. In an increasingly networked world in the wake of Industry 4.0 and the Internet of Things (IOT), however, the two worlds are growing ever closer together. Find out below how a common security approach can be created.
IT versus OT
IT (Information Technology) describes all technologies for data processing by means of software. According to Gartner, Operational Technology (OT) is “hardware and software that detect or cause change by directly monitoring and/or controlling physical devices, processes, and events in the enterprise.”
The OT area can be further divided into different areas. For example, a distinction can be made between the areas of building control or automation (access control, video surveillance, intrusion alarm systems, fire alarm systems, etc.) or production plants (production lines, filling plants, etc.).
Whereas in OT the topic of security is primarily availability, in IT one speaks more of terms such as confidentiality and integrity. This difference in focus often results in a conflict between the defined goals and how they are to be implemented.
Furthermore, there is a serious difference in the planning and life cycles of the technologies used. While IT usually works with a planning cycle of 3-5 years, building control or production environments are planned with a life cycle of 10 and significantly more years. This also applies to the control technology (OT) used.
IT and OT pose complex security challenges for companies
While for a long time areas such as building automation or production (OT) were encapsulated system landscapes, with increasing digitization they are growing ever closer together with classic information technology (IT). The increasing networking of devices and machines with the infrastructure and the Internet requires convergence between IT and OT, especially with regard to the issue of IT security. In order to successfully implement digitization projects, it is not only technical measures that are important, but also changes to the organizational structure and clear definitions and responsibilities.
How to create a unified security approach for IT and OT infrastructures
With a Security Information and Event Management (SIEM) it is possible to keep an eye on both worlds with regard to a holistic security view. With a SIEM, a company or organization is able to detect and defend against threats and attacks on its IT systems, even if no preventive measures are technically possible. And it does so before any damage can have a lasting impact on business operations or bring them to a standstill. In addition, a SIEM continuously improves the security, compliance and quality of IT systems during operation. With the help of a SIEM, the systems are continuously and automatically monitored for security-relevant incidents.
Security Use Cases as the Basis for a Successful SIEM
A key pillar of a SIEM is the security use cases (security or risk scenarios) that are to be monitored using a SIEM solution. Because as different as IT infrastructures are, as different are the compliance requirements as well as the risk management of the individual companies. This means that the use cases must always be adapted to the respective environment and infrastructure.
Examples of use cases from the IT environment are:
- Direct reading of large amounts of data from a database bypassing the application server
Risk description: If users read data directly from a database, it is possible to bypass any access controls of the overlying application. It should only be possible for the overlying application to read data from the databases, taking rights management into account.
- Suspicious communication with known infected IP addresses
Risk description: If a system attempts to call a known, infected malware address, it can be assumed that this host has been infected by malware not previously detected by the virus scanner.
- Unexpected configuration change on safety-relevant systems
Risk description: Configuration files on security-relevant systems tend to be static and are only changed infrequently and if as part of a change request. Changes to password settings or important configuration files can indicate compromise of the system and lead to loss of data or system availability.
- Use of privileged accounts
Risk description: privileged accounts have extended rights that can be used to cause a great deal of damage to IT and OT systems. The use of these accounts must therefore be controlled.
Information source for a SIEM can of course also be events from the OT. Certain events or combinations of events can also indicate a security incident here. The risk scenarios to be monitored for a SIEM are developed as part of a risk analysis.
Examples of use cases from the OT environment building control/automation are:
- Multiple entry into the building/premises with the same access card without first leaving the building/premises again with this access card.
Risk description: Multiple access with the same access card raises the suspicion of misuse. In this way, it is possible for unauthorized persons or now unauthorized former employees to gain access to the building/premises.
- Multiple access attempt from an unusual place
Risk description: An employee attempts to gain access to an area/building/premises to which he/she does not actually have access. Even if this is initially a failed attempt, it makes sense to follow up on it in order to be able to track any further actions by the person.
- Violation of the “multiple eyes” principle
Risk description: For high-security areas, a 4-eyes or even 6-eyes principle often applies. This means that there must be at least two or 3 people in these rooms/areas. If one of these persons leaves the room/area and does not return within a certain time (e.g. 5 minutes), then the risk of an unsupervised act arises.
- Control of data flows.
Risk description: To secure proprietary OT systems, it is necessary that the OT network is protected and only the communication that is required for production takes place. Increased data volume may indicate an anomaly / attack and must be alerted.
If one of these scenarios is identified in the SIEM in the collected data, an alert occurs and a security analyst immediately takes care of this incident.
As an extension to the SIEM solution, SOAR (Security Orchestration, Automation and Response) solutions provide critical benefits for operational efficiency. SOAR describes software and processes to improve threat and vulnerability management in an organization. By automating and orchestrating on prioritized high-risk threats, SOAR can save critical time.
Managed Security Services
There are many reasons for outsourcing IT security (Managed Security Services). IT landscapes are becoming increasingly complex, so that most companies have neither the know-how nor the human resources available. In addition, costs become calculable, corresponding recurring trainings are no longer necessary and there is more time for company growth.
About ConSecur GmbH
ConSecur GmbH, founded in 1999 and based in Meppen, is a management consultancy for information security: ConSecur develops, analyzes and implements security concepts for information processing. In addition, ConSecur evaluates and improves existing security concepts, trains users and experts, and advises its customers on the selection of IT security components in a vendor-neutral manner.
ConSecur’s particular focus is on the conceptual design and development of Cyber Defense Centers (CDC) and the establishment of Security Information and Event Management (SIEM). ConSecur operates its own Cyber Defense Center in Bochum, where it offers managed SIEM services to its customers.
About CoreWillSoft
In 2017, CoreWillSoft GmbH was founded and since then has been passionate about bringing product and security innovation to the access and operations technology industry.
Their corporate vision is to make complex security solutions easily available to every user, regardless of age or IT affinity.
With its innovative SECUSE approach, CoreWillSoft can simplify concepts such as building management, granting wireless access and mobile payments, and enable them with just a few clicks.
CoreWillSoft ensures the highest level of data security and privacy by integrating the biometric enrollment, device binding and hardening concepts to keep data secure.